Turning the Table on the Trackers: Wikileaks Sniffs out Spy Salesmen
What was Mostapha Maanna of Hacking Team, an Italian surveillance company, doing on his three trips to Saudi Arabia in the last year? A new data trove from WikiLeaks reveals travel details for salesmen like Maanna who hawk electronic technology to track communications by individuals without their knowledge.
Other examples include - Stephan Oelkers, a top executive at the Gamma Group, an Anglo-German rival, who made three trips to Uganda in early January this year, and again in late May, followed by a trip in mid July and Avner Turniansky, from the Israeli company Verint, who traveled to Nigeria in April.
Given that Maanna, Oelkers and Turniansky share the same occupation - selling spy software to government law enforcement agencies - it would be reasonable to speculate that the three men did not make these trips purely for sight seeing.
All three individuals work for companies that boast about their ability to monitor suspects by following mobile phones, intercepting emails and analyzing social media, so it is perhaps more than a little embarrassing that their own staff have been tracked by activists, effectively turning the tables on them.
Julian Assange, the editor in chief of WikiLeaks, says that the information came from a special counter-intelligence unit that his organization created "to protect WikiLeaks' assets, staff and sources from hostile intelligence operations and to reveal the nature of intelligence threats against journalists and sources more broadly."
Wikileaks suspects that many buyers use these technologies to snoop on activists and dissidents. Certainly the technology that Gamma, Hacking Team and Verint offer for sale would allow such surveillance.
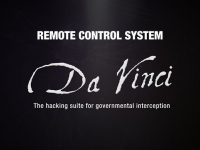
According to research conducted by the Kaspersky Lab, an anti-virus company, Hacking Team sells technology that can be used to create emails to target suspects by inviting them to click on a link or attachment that then installs a spy tool called Remote Control System (RCS) on the target's computer.
RCS (also known as DaVinci) can then copy the Web browsing history of its targets, turn on their computer microphone and webcam to eavesdrop on them, as well record their conversations on computer applications like Skype.
Middle Eastern Travels
Maanna, whose LinkedIn profile confirms that he works for Hacking Team in Milan, completed high school in Tyre, Lebanon, before moving to Turin, Italy, to do an undergraduate and graduate degree in telecommunications engineering. After finishing his degrees, he worked for two years at Nokia Siemens Network, where he sold mobile data technologies to companies like T-Mobile in the Czech republic and Germany and Orange in Spain and the UK, before he jumped ship to come to the Italian company in January 2011.
In addition to three trips to Saudi Arabia, Maanna's travel profile places him in Egypt three times in 2013, as well as making two trips each to Malaysia and Morocco in the last three years, among other countries like United Arab Emirates (UAE) and Turkey.
Marco Bettini, a sales manager for almost ten years at HackingTeam whose LinkedIn profile says he studied at the Istituto Radiotecnico Beltrami, is also identified as traveling to Morocco and UAE in February 2013.
Activists Targeted
Hacking Team has come under fire for the alleged use of its software in Morocco, Turkey and the UAE.
Mamfakinch, a Moroccan citizen journalist group that was created during the 2011 Arab Spring, believes that it was targeted with a "backdoor" attack by software that is identical to Hacking Team's RCS system, according to an analysis by Dr. Web, an anti-virus company. Slate Magazine described how the organization's computers were infected by spy software after members opening an email titled "Dénonciation" (denunciation) that contained a link to what appeared to be a Microsoft Word document labeled "scandale (2).doc" alongside a single line of text in French, which translates as: "Please do not mention my name or anything else, I don't want any problems."
And Wired magazine recently published details of an attack on a U.S. activist who was sent an email about Turkey that appeared to come from a trusted colleague at Harvard that "referenced a subject that was a hot-button issue for the recipient, including a link to a website where she could obtain more information about it." Although she did not click on the email, Arsenal Consulting, a digital forensics company, analyzed the link and discovered that it too contained RCS attack software.
Citizen Lab, a computer security research group in Canada, has also identified emails sent to Ahmed Mansoor, a UAE human rights activist, that was also allegedly designed with Hacking Team software. Mansoor was a member of a group of activists who were imprisoned from April to November 2011 on charges of insulting an Emirati royal family. He told Bloomberg that he was identified and then beaten after he clicked on an email that contained a Microsoft attachment that infected him with the spy software.
Company Response
Hacking Team says that they strictly follow applicable export laws and other regulations and only sell their products to governments or government agencies.
"The point that is generally missed in discussions like this is that the world is a dangerous place, with plenty of criminals and terrorists using modern Internet and mobil technologies to do their business, and that threatens us all," Eric Rabe, the general
counsel of Hacking Team, told CorpWatch via email. "We firmly believe that the technology we make available to government
and law enforcement makes it harder for those criminals and terrorists
to operate." Rabe said that his company also understands the potential for abuse of their products, so they review customers before a sale to determine whether or not there is "objective evidence or credible concerns that Hacking Team technology provided to the customer will be used to facilitate human rights violations."
Rabe said that his company also understands the potential for abuse of their products, so they review customers before a sale to determine whether or not there is "objective evidence or credible concerns that Hacking Team technology provided to the customer will be used to facilitate human rights violations."
The company also notes that their products have an auditing feature that cannot be turned off so that agencies can check how and when surveillance occurs. "Of course, HT cannot monitor the use of our software directly since clients must have the ability to conduct confidential investigations," Rabe adds. "Should we suspect that abuse has occurred, we investigate. If we find our contracts have been violated or other abuse has occurred, we have the option to suspend support for the software. Without support, the software is quickly rendered ineffective."
Rabe says that Hacking Team did investigate "the Morocco and UAE
assertions" but he was not able to comment since the company "does not
share the results of such investigations nor do we publish whatever
actions we may subsequently take."
Activists still say that they are very concerned about details in the travel logs released by Wikileaks. "The evidence and timeline does give credence to the idea that the discovery of Hacking Team software in Morocco and UAE, corroborates with their Sales Team visit to those countries," Kenneth Page, a policy officer at Privacy International, told CorpWatch.
Profiting Off the Suffering of Individuals
Wikileaks also published the travel schedule of several employees of Gamma International, a UK company with offices in Germany, that sells a technology named FinFisher that also claims that it can track locations of cell phones, break encryption to steal social media passwords, record calls including Skype chats, remotely operate built-in web cams and microphones on computers and even log every keystroke made by a user. (See related story "Turkmenistan and Oman Negotiated to Buy Spy Software: Wikileaks")
Some of the trips made by Gamma employees that were identified by Wikileaks are easy to match up such as those made by Brydon Nelson, the managing director of G2 - a Gamma Group company that conducts government surveillance training - because he blogs publicly about his travels and even hints at his profession by mentioning that he attended the 2012 general assembly of the International Criminal Police Organization (Interpol) and stayed at the Hotel Cavalieri in Rome.
Other travel schedules - such as those of Oelkers to Uganda - are hard to verify. The company did not respond to requests for comment by press time.
Human Rights Watch has this to say about Uganda: "After 26 years of President Yoweri Museveni's rule, ongoing threats to freedom of expression, assembly, and association continue to raise serious concerns. Security forces largely enjoy impunity for torture, extrajudicial killings, and the deaths of at least 49 people during protests in 2009 and 2011."
In the last year, however, Uganda has not cracked down on online organizing: "Unlike in the previous year, there were no reports the government attempted to restrict access to the Internet," says the latest the U.S. State department report on human rights report on the country. "Individuals and groups could generally engage in the expression of views via the Internet, including by e-mail."
Could this change if Uganda buys sophisticated tools from Gamma to allow it to track dissidents? That is what groups like Privacy International are concerned about.
"This is clearly not an ad-hoc process within a small industry, but a calculated and considered business deal in a global trade with profits made off the suffering of individuals," says Page. "As the Wikileaks release today has shown, the business procedure behind the sale of surveillance technology is as well laid out as any other international trade - including proposals and presentations, site and country visits, contracts, and costing packages."
Page said that the companies that develop and sell surveillance technology to such regimes should not be allowed to abdicate responsibility for freely selling this technology to just any government regardless of their human rights record.
"Companies know full well how their products work and, after tailoring to their specific clients need, know how they will be used," added Page.
* This article was amended on September 6, 2013, to add the response from Eric Rabe of Hacking Team
- 116 Human Rights